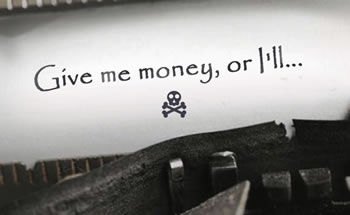
So I got an email this morning from some person or persons unknown stating that on such-and-such a date, I visited such-and-such a pornographic website–and unless I pay them off in Bitcoin–uh-huh: like I have any Bitcoin, or know what it is, or care–they’ll tell all my friends and everybody else who knows me. They also claimed I used such-and-such a password, but the password they cited belongs to no one I know of.
What we have here is a criminal offense: attempted blackmail. We are advised to delete the message and run a virus scan, which we have done.
There are a jillion porn sites on the Internet and it’s not hard to stumble onto one of them while looking for something else. All it takes, sometimes, is the smallest of typos. So the blackmailers are on pretty firm ground there: just about everyone has visited a porn site, if you count accidents as visits.
Now, why didn’t we call the police? Only because I doubt the cops could catch these vermin. If they could be caught, they’d have been caught already.
If you receive one of these messages, don’t be afraid. Just delete it and run a virus scan. It would probably be most unwise to reply to the message in any way. So please don’t do that!
Good advice, Lee. All computers have an IP address that is visible across the Internet. If you want to see that address, just type “what’s my IP” into a search engine and you’ll see an address, probably four groups of 1-3 numbers, separated by periods (an IPv4 address) but possibly a much longer IPv6 address. That is a unique address and, in theory, could be used to trace back to your computer. However, that address is translated once, or many times along the way and could be “overloaded”, which is to say that many devices use a single IP address, but have unique port numbers (which are subdivisions which allow an IP to be divided into unique session identities). The IP address your computer has locally is very unlikely to be the IP address seen if you type what’s my ip into a search engine.
In theory, if everyone along the way is maintaining their log files, you could piece together a session and trace someone’s activity. If a serious crime is involved, that may actually happen, but firsthand experience has taught me that it is hit or miss. The law enforcement world pursues child pornography violations as perhaps murders, but little else. Frequently the law enforcement people do not understand the technical aspect of the matter and will pursue hunches. On more than one occasion, when cooperating with investigators, they seem to gravitate to theories of “inside jobs”, even though I had provided them with verifiable records showing that the email or phone call in question came from the outside.
Theory and practice also diverge because it’s possible to go to proxy sites and relay your web traffic through them and mask your actual IP. Internet criminals use these proxy sites often and in many cases it becomes impractical to trace activity because of these. Many of the proxies are outside the jurisdiction of the US and are not inclined to cooperate with the authorities.
Beyond that, law enforcement is not inclined to take much of an interest in petty crimes. I once had occasion to speak to an FBI officer about this matter and came away with the impression that if the amount was under $50,000 they were not likely to get involved, even if the matter was directly under Federal jurisdiction. The last time I cooperated with law enforcement on a matter, it involved several thousand dollars and while there was significant interest at the local level, I got the impression that the local police were not getting a lot of help or cooperation in tracing the source identification I had given them.
The criminal you encounter on the Internet may be next door, or quite possibly in another state, country or continent. Criminal activities in unfriendly nations can be very hard to combat. Spam sources, most likely from China, are a major headache for administrators of online fora and blogs. Internet cafes in Third World countries are almost impossible to trace.
But as I stated above, your advice is quite good, Lee. I’ll add that Malware Bytes is a great solution to many forms of malware. It’s a good idea to keep that name written down. Also, it’s a good idea to have more than one browser on your computer, because a browser hijack which disables your main browser may not affect your other browsers, giving you a way to reach online help, such as Malware Bytes.
We’ve got Malware Bytes.
I couldn’t understand most of what you’ve said, but there should be many others reading it, and I’m sure you’ve helped them: thank you.
To distill matters; it’s possible to track online activity aimed at defrauding the innocent, but in practical terms it’s not likely to happen.
If it was likely that they’d catch these villains, we wouldn’t be seeing so much villainy.
From what I can tell, many of them are in India, China, or somewhere nearby to those places. I’ve actually engaged phone scammers in conversations and suggested to one that he pursue technical education and enter the legitimate workforce. He was surprisingly contrite.
What are they talking about? If a person has HBO or Cinemax or one of those other pay channels you have pornography. By watching some of the commercials on regular TV you are watching borderline soft pornography. Pompei has nothing on the Western world. And the people who have brought us this pornographic culture are the ones behind the #MeToo Movement. Is this world a crazy place, or what?
Don’t you love that weird teaming-up of the hookup culture with #MeToo neo-wowserism.
It amazes me that, according to the Left, any and all sexual conduct is morally acceptable, yet they will claim sexual abuse, etc. at the drop of a hat.
It’s #MeToo + Hookup Culture = Far Left Crazy
So much internet scams out there